What does the word 'hacker' mean and how does it connect to telephony?
Did you know that hacking and telephony share a fascinating piece of history? The connection between the two became very strong when telephony got more automated in the mid-1900s, making almost every phone a point of access to a global network of explorers.
This needs patching
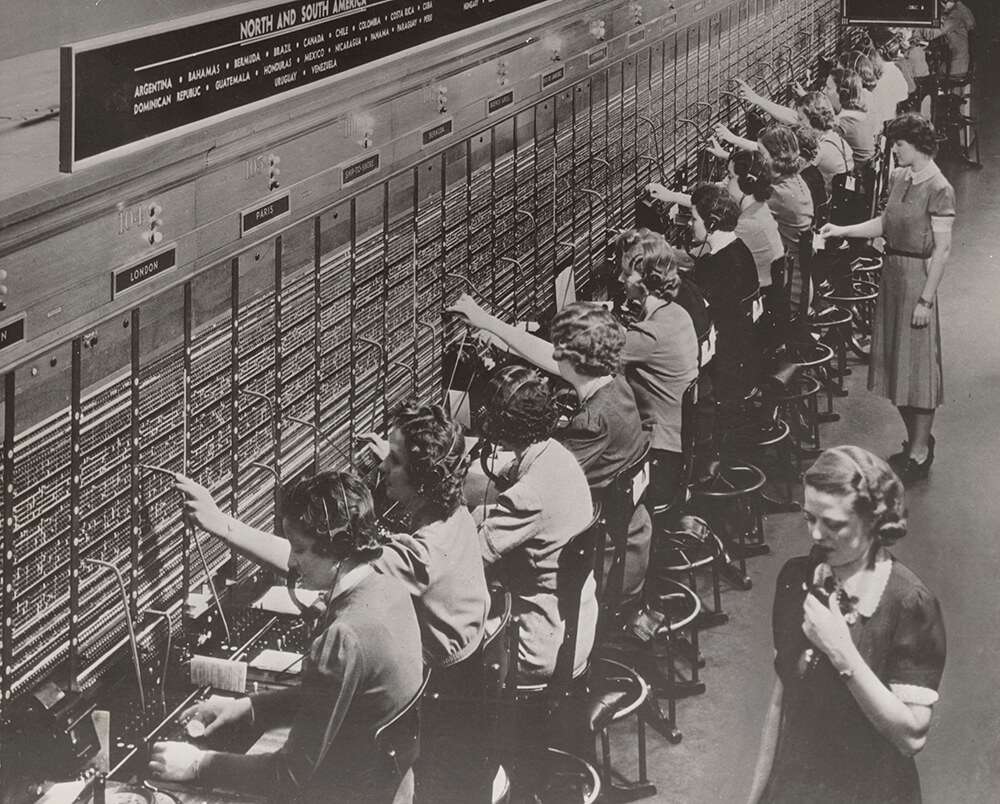
Information security is a very important subject nowadays, but this wasn’t always the case. An example of this is the early development of telephony when little attention was given to security features. It wasn’t a big deal, mostly because, at that time, all of the call routing was done by humans.
Calling worked quite a bit differently then: you couldn’t just dial a number to call someone. Instead, you had to call an operator first and tell them who you wanted to reach, and the operator would take care of patching the call to your requested destination. Furthermore, telephony was an expensive luxury in the day, and experimenting would cost a lot of money. As a result, there weren’t a lot of possibilities to explore the technical limits of telephony at that point.
Telephony became more and more popular in the early 1900s, and consequently, the number of operators needed to be increased, as well as the number of (internationally) connected networks. This made telephone companies eager to find ways to reduce their costs. Additionally, there were concerns about privacy, since operators would be able to tap into the calls they were routing easily and without being detected.
Operators would continue to form an important element of the telephony networks for a while, but from 1920 onwards, telephone companies started deploying solutions to make humans unnecessary in the day-to-day calling process.
With the adoption of Direct Dialling (dialling a number using a phone with a rotary dial or dial pad), humans were taken out of the equation and the task of patching calls was automated. Now that call costs dropped a bit, and wages went up, telephony came in reach of even more people. Payphones appeared in the streets.
Calling become a lot cheaper than it used it be, but that wasn’t to say it was very cheap. The bigger the distance between the caller and callee, the more you had to pay. This meant an interstate call in the US in the sixties could cost $4 for a 5-minute call, which is roughly $34 (roughly EUR 30) in 2018 if you correct for inflation.
Nevertheless, the fact that telephony became mainstream inspired a lot of bright minds to explore the now automated telephone exchanges, and see if they could be tricked for both fun as well as profit.
Hackers, phreaks & mobsters
The term “hacker” is thought to originate from the grounds of the renowned research university MIT (Massachusetts Institute of Technology) because one of the earliest recorded uses of the word “hacker” is a 1963 article in MIT’s The Tech newspaper, titled “Telephone hackers active”. These phone hackers were also called phreaks or phreakers, which is a contraction of “phone” and “freaks”.
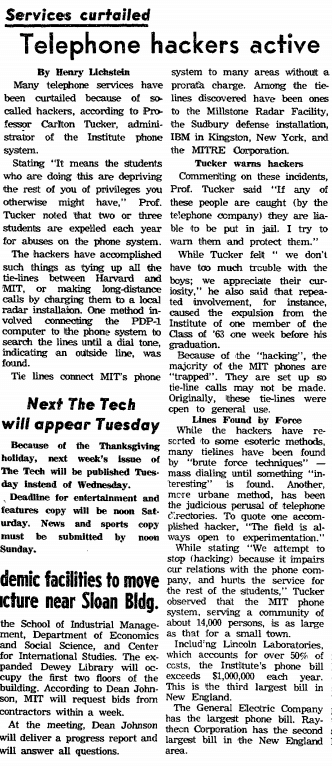
The article mentions “making long-distance calls by charging them to a local radar installation” and several other (local) telephone lines that could be used to relay a call. This would prevent the original caller from being charged high (long-distance) calling rates. The open relay lines were found using a technique that is now known as “war dialling,” in which a computer is set up to simply call every number in a telephone number block consecutively, until something interesting is found. This way, hackers were exploring a worldwide phone network and trying to discover new things.
The students at MIT (and other explorers throughout the world) were not the only ones to discover vulnerabilities in telephones’ system security though. Criminals where equally interested, be it for a very different goal. They got help from an unexpected source, named Walter L. Shaw: a telecom engineer and inventor who worked for the Bell Telephone company. While working at Bell, he invented some key telephone functions that we cannot live without today, such as call forwarding and conference calling. Mr Shaw left the company after 14 years because there was a strong disagreement over who held the rights and patents over his inventions.
Looking for new ways to make money, Shaw turned to the mafia. His knowledge of phone systems helped him create a device called a “blue box,” which allowed the mafia to make free and untraceable long-distance calls.
For fun and profit
The newly invented device, consisting of a keypad (similar to that on a phone) wired up to a speaker, cleverly took advantage of the security shortcomings of the telephone exchanges. Back then, exchanges would communicate with each other using audio signals to start, route and end calls. Because the exchange systems had no checks in place to verify the control tones were coming from an actual exchange, every person with a phone and a blue box could manipulate the exchange into doing things that were normally reserved for other exchanges. All you needed to do was place the blue box speaker on the microphone of the phone headset, and send specific combinations of tones by pressing the keys on the keypad to control the exchange.
Tones generated by a blue box can best be imagined as similar (but not completely equal) to the DTMF tones produced by modern phones when you press keys on the dial pad. One crucial tone is that of 2600 Hz. It was important for blue box users at the time because it would signal a telephone exchange that a call had ended without actually terminating the control line to the exchange. This, in turn, meant that the exchange would be momentarily left vulnerable to new instructions.
Making a toll-free call with a blue box would typically go like this:
- Put a fresh battery in your blue box.
- As an extra precaution, don’t use your home phone but instead find a payphone as your entry point.
- Lift the headset, switch the blue box on and place the speaker on the payphones’ microphone.
- Dial a toll-free number using the dial pad of the payphone.
- As soon as your call is answered, quickly press the button on top of the blue box to generate a 2600 Hz tone. The call to the toll-free number will drop.
- Within 10 seconds after the call is dropped, the dial pad on the blue box should be used to dial a telephone number one would normally pay for. The telephone exchange will process the tones from the blue box as if they came from a legit source.
- The call is like any other normal call. On hang up, the system in charge of billing will record a call to a toll-free number.
An unlikely connection
You didn’t have to have a lot of inside knowledge on phone systems to discover the 2600 Hz tone was special. It is said that several people discovered this by themselves simply because they were whistling a particular song while on the phone and would get disconnected as a result. One phreaker by the name of John Draper made an interesting discovery after having some breakfast cereal. A toy whistle included in boxes of Cap’n Crunch cereal would generate a perfect 2600 Hz tone when one of the two whistles’ holes was covered. Because of this discovery, he subsequently adopted the nickname “Captain Crunch”.
Captain Crunch became a very well-known phreaker. In 1971 he was Slate’s Use of Your Data interviewed by a journalist from the lifestyle magazine Esquire, revealing details on the techniques phreakers used, and admitting to producing and selling a 1000 blue boxes to a group of criminals for $300.000 in cash. The interview drew the interest of the FBI, who had started cracking down on phreakers at that time. Although the article only mentioned Drapers’ nickname, this wasn’t enough to prevent him from being arrested and sentenced to five years of probation.
It was not just the FBI who was interested. Among the readers of the Esquire article were Steve Wozniak and Steve Jobs, who would later become the founders of Apple. Wozniak invited Captain Crunch to his dorm room where they exchanged circuit board designs and technical details. They ended up producing several dozens of blue boxes which were reportedly mostly sold to Hollywood stars, after making friends with several phreakers in Los Angeles. Indeed, Steve Jobs first company was selling illegal goods!
A shared history
Can one still use a blue box today? Well, unfortunately not. Phreaking slowly became more popular during the 70’s, which in turn prompted telephone network operators to put effort into developing countermeasures against several different exploits discovered by hackers over the years. With the most obvious holes covered, this meant that most of blue boxing came to an end in the 80’s.
What has not gone, however, is the enduring fascination of hackers with all kinds of technical systems and how they can be explored and pushed to their limits, persuaded to do things they were not designed to do.
Phreaking was one of the things that brought the idea of hacking to a greater public, which in turn inspired many people to start discovering and share their knowledge freely. A fundamental principle, important today, made popular with the help of telephony.
Subscribe to Talksome blog
Get the latest posts delivered right to your inbox
